Florida-Based Elections Software Company Denies Systems Were Hacked
Follow CBSMIAMI.COM: Facebook | Twitter
ORLANDO (CBSMiami/AP) — The chief operating officer of a Florida-based company which provides voter registration software is refuting parts of a leaked U.S. National Security Agency report which suggested their systems were hacked to send phishing messages to local elections officials nationwide.
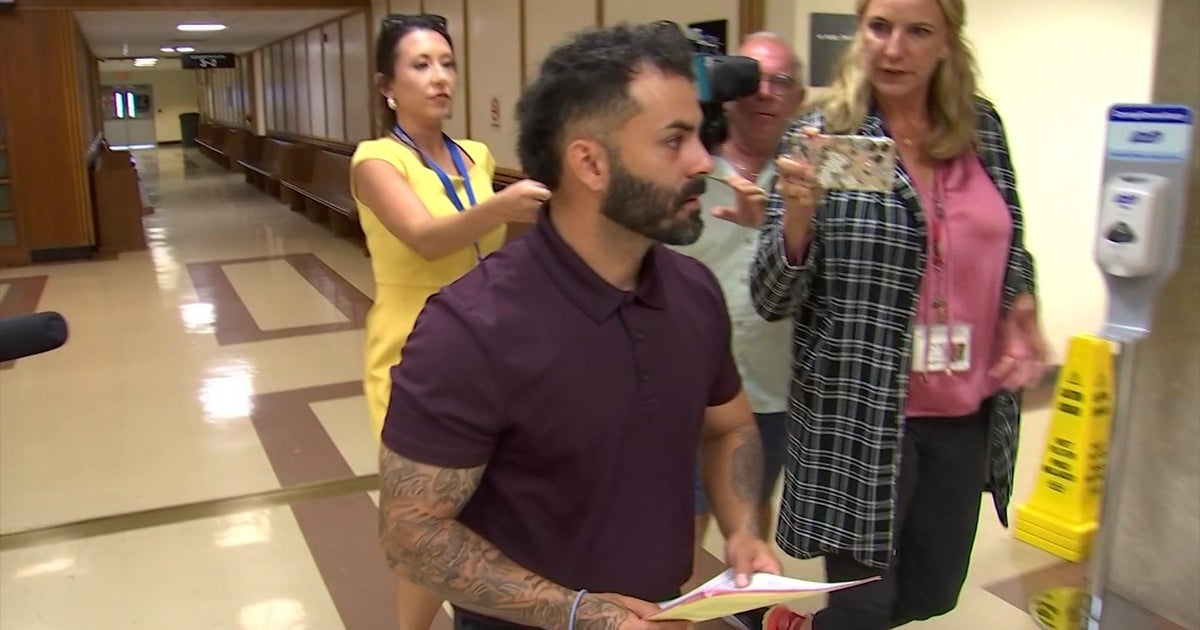
VR Systems' Ben Martin told Florida election supervisors during a presentation Monday that his company's systems were never breached.
"We have no indication that they got anywhere close to our systems," Martin said. "They never got into our systems."
Martin gave a rundown of events from last year leading up to the leak earlier this month of the NSA report.
The report said information from VR Systems was used to send phishing emails to 122 local election officials just before the election last November, in an attempt to break into their systems. So far, there is no indication that voting or ballot counting in any states were affected.
"When something like this happens, it hurts us and hurts us as an elections community," VR Systems CEO Mindy Perkins told supervisors at the Florida State Association of Supervisors of Elections conference outside Orlando on Monday. Many of the supervisors use VR Systems software.
In March 2016, law enforcement officials notified elections officials and vendors about a series of suspicious IP addresses and advised them to make sure no communications was sent from them.
"It doesn't mean that anybody got in our system, it just meant that those IP addresses were looking," Martin said. "They were looking for open doors. They were looking for back doors and ways to go in."
Five months later in August 2016, VR Systems received a series of phishing emails.
"What they wanted was for my staff or us to open those emails, which they believed would give them access to our email addresses, and then they could send emails looking like they came from us," Martin said.
The first email was spotted by a company computer scientist who recognized it as suspicious, and the emails were quarantined and never opened by anybody at the company, Martin said.
Two months later, right before November's election, a customer called the company to report he had received a suspicious phishing email that appeared to have come from VR Systems, but upon closer examination, it was an email trying to appear like it came from the company.
Company officials immediately called election supervisors and sent out written warnings to their customers not to open emails from that address.
Martin acknowledged that some supervisors and customers didn't receive the warnings, but he said it likely ended up in their spam folders.
Some election supervisors were nevertheless concerned about how the sender of the phishing emails had gotten their email addresses.
"There are a couple of missing links here," said Craig Latimer, Supervisor of Elections for Hillsborough County in Tampa, whose office had gotten the phishing emails.
"We don't know who got the emails. They didn't come from us. I have no way of knowing where they went to," said Martin, who added that law enforcement had told him that all of the email addresses of the 122 local officials were publicly available on their websites. "They could have gotten them off the internet, just searching after they had identified our customers."
(© Copyright 2017 CBS Broadcasting Inc. All Rights Reserved. The Associated Press contributed to this report